Deconstructing the Hiya Authenticity Score: A Security Analyst's Perspective
I spent four years in the trenches of a telecom fraud operations center, listening to the heartbreak of elderly victims who had their life savings wiped out by a "grandson" on the phone. Back then, it was mostly social engineering—scripts, urgency, and a little bit of psychological pressure. Today, the landscape has fundamentally shifted. We aren’t just fighting human liars; we are fighting mathematical models that can synthesize human emotion at scale.

McKinsey recently reported that over 40% of organizations encountered at least one AI-generated audio attack or scam in the past year. That is not just a rounding error; it is a systemic crisis. In my current role at a fintech, we get pitched "AI-driven detection" tools every Tuesday morning. Sales reps love to drop terms like "authenticity score" and "perfect detection" like they’re magic spells. I don't buy magic. I buy engineering.
The First Question: Where Does the Audio Go?
Before I care about how a vendor calculates an authenticity score, I need to know where the data goes. If you are sending your customer’s voice stream to a third-party cloud API for "real-time analysis," you have just created a massive compliance and privacy liability. Is it encrypted at rest? Who has access to the metadata? Is the audio stored to train their next-generation model? If a vendor tells you "the data is anonymized," ask them how they handle the PII (Personally Identifiable Information) inherent in the biometric signature of a human voice. If they can’t answer, the demo is over.
What Actually Makes Up an Authenticity Score?
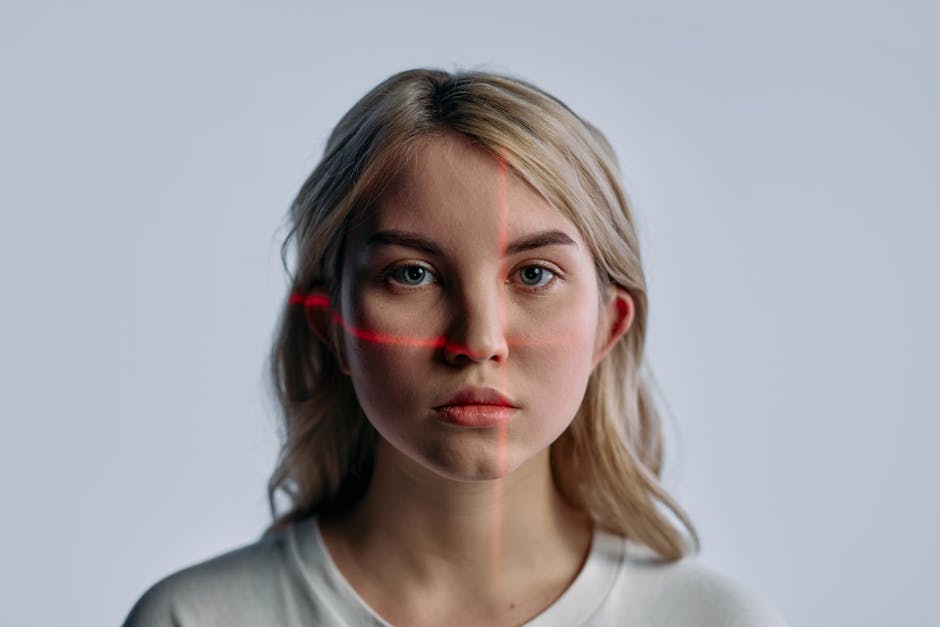
When Hiya (or any provider in this space) generates an authenticity score, they aren't looking for a "lie detector" light. They are looking for mathematical artifacts— voice deepfake signals—that reveal the seams where reality ends and the GAN (Generative Adversarial Network) begins.
To calculate these scores, engines typically analyze several vectors:
- Spectral Analysis: AI models often struggle to replicate the full frequency spectrum of human speech. You might see a "cutoff" or unnatural smoothing in high-frequency bands where the generative model opted for efficiency over fidelity.
- Prosody and Cadence: Real humans have jagged, erratic breathing and micro-pauses. AI, even advanced models, often has a "rhythmic stability" that is too perfect, too steady, or strangely robotic in the way it handles syllable duration.
- Latent Space Anomalies: This is the "ghost in the machine." By analyzing the latent representation of the audio, tools can look for patterns that don't match human vocal tract physics.
- Environment-Signal Mismatch: If the background noise sounds like an office, but the spectral fingerprint of the speech shows the hallmarks of a specific VQ-VAE model, the authenticity score should tank.
The "Bad Audio" Checklist
If you’re evaluating a vendor, you need to test them against the reality of a call center. Marketing demos use pristine studio audio. Real fraud happens in a messy, low-bandwidth environment. Before you trust any score, put their engine through this gauntlet:
Scenario Why it breaks bad detectors G.711/G.729 Codec Compression Aggressive compression scrubs the very artifacts the AI is trying to detect. Overlapping Background Noise Crowd noise often masks the high-frequency spectral clues of AI generation. Multiple Transcoding If a signal moves from a VoIP app to a cellular network, the noise floor changes, often "cleaning" or "blurring" the deepfake signature. Intentional Low-Fidelity Attackers are learning to intentionally downsample audio to bypass high-end detectors.
Deployment Architectures: Real-Time vs. Batch
There is a massive trade-off between real-time analysis and batch processing. Understanding this is crucial for your architecture.
1. Real-Time Analysis
This happens inline during the call. The trade-off here is latency. If the analysis takes too long, you introduce jitter into the call, which makes the voice sound unnatural, essentially creating a "bad audio" artifact yourself. If your tool adds more than 100-200ms of latency, your users will hang up. Real-time tools usually run lighter, faster models—which often means they are less sensitive to sophisticated, subtle deepfakes.
2. Batch Analysis
This is for post-mortem forensics or non-critical path validation. Here, you can afford to run heavy models, multi-pass spectral analysis, and cross-reference against known attack vectors. This is where you catch the pro-level stuff. I prefer a tiered approach: real-time for immediate session flagging, and batch for deep-dive investigation.
The Accuracy Myth: Why "99% Accurate" is Garbage
Whenever a vendor tells me their system is "99% accurate," I ask for the conditions of that claim. This reminds me of something that happened made a mistake that cost them thousands.. 99% accuracy on what dataset? Was it tested against zero-day deepfakes, or was it tested against two-year-old models that sound like text-to-speech from 2018?
You ever wonder why accuracy without context is a lie. If you have a high False Positive Rate (FPR), you are going to alienate your customers by blocking legitimate transactions or calls. If you have a high False Negative Rate (FNR), you are letting the vishing attack through. I would much rather have a 90% accurate system that clearly labels its "confidence interval" than a 99% system that is a enterprise voice security solutions 2026 black box.
A good authenticity score should be treated as a probability, not a binary "Yes/No." When a vendor tells you to "just trust the AI," run. You trust the data. You trust the process. You verify the results.
The Landscape of Detection Tools
To keep my infrastructure secure, I categorize tools based on where they live in the the stack:
- API-Based Detectors: Easy to integrate, but you are effectively outsourcing your security and your data. Requires strict contract review.
- Browser Extensions/Client-Side: Great for end-user protection, but easily bypassed if the fraud happens at the network gateway level.
- On-Device Analysis: Excellent for privacy, but limited by the compute power of the end-user device. Not feasible for call center infrastructure.
- On-Prem Forensic Platforms: The "Gold Standard" for enterprise. You control the hardware, the models, and the data. It is expensive and requires a team to maintain, but it’s the only way to avoid the "Where does the audio go?" headache.
Conclusion
Deepfake technology is moving faster than our defensive measures. The McKinsey statistic proves we are already in the middle of a surge, not approaching one. When you look at an authenticity score, remember that it is a heuristic, not a truth. It is a mathematical guess based on the probability of a signal being generated by a machine.
Ask the hard questions. Don't let the sales team gloss over the "bad audio" edge cases. Demand to see how the model behaves when the signal is noisy, compressed, or transcoded. If they can’t show you the math behind the score, they aren’t selling security—they’re selling a false sense of peace of mind. And in the world of incident response, peace of mind is just an oversight waiting to happen.